Invisible wars
It is not new today, but now it is taking on a dimension never seen before–war is not only waged with military hardware or heavy weaponry. Alongside this or even in anticipation of military intervention, a war is taking place on several fronts that nobody sees and that uses other types of weapons: the cyber ones. The power of destruction has been known for years, but with Russia’s invasion of Ukraine the cyber war is taking on proportions never seen before.
So, it is understandable that the US Department of Homeland Security has already warned all sectors of government, from the largest to the smallest, to pay special attention to the vulnerabilities in their systems and improve their physical and digital resilience. But it’s not just the US that is at risk. In fact, all countries siding with Ukraine, which means the member states of NATO, including Canada, and the European Union, are also on digital alert.
On the other hand, after the Russians entered Ukraine, the group Anonymous published a statement on the social platform Twitter, communicating that, for peace, they would try to attack Russian infrastructure in order to weaken them. Hours later, they announced they had taken down the Kremlin website and other Russian websites were attacked thereafter.
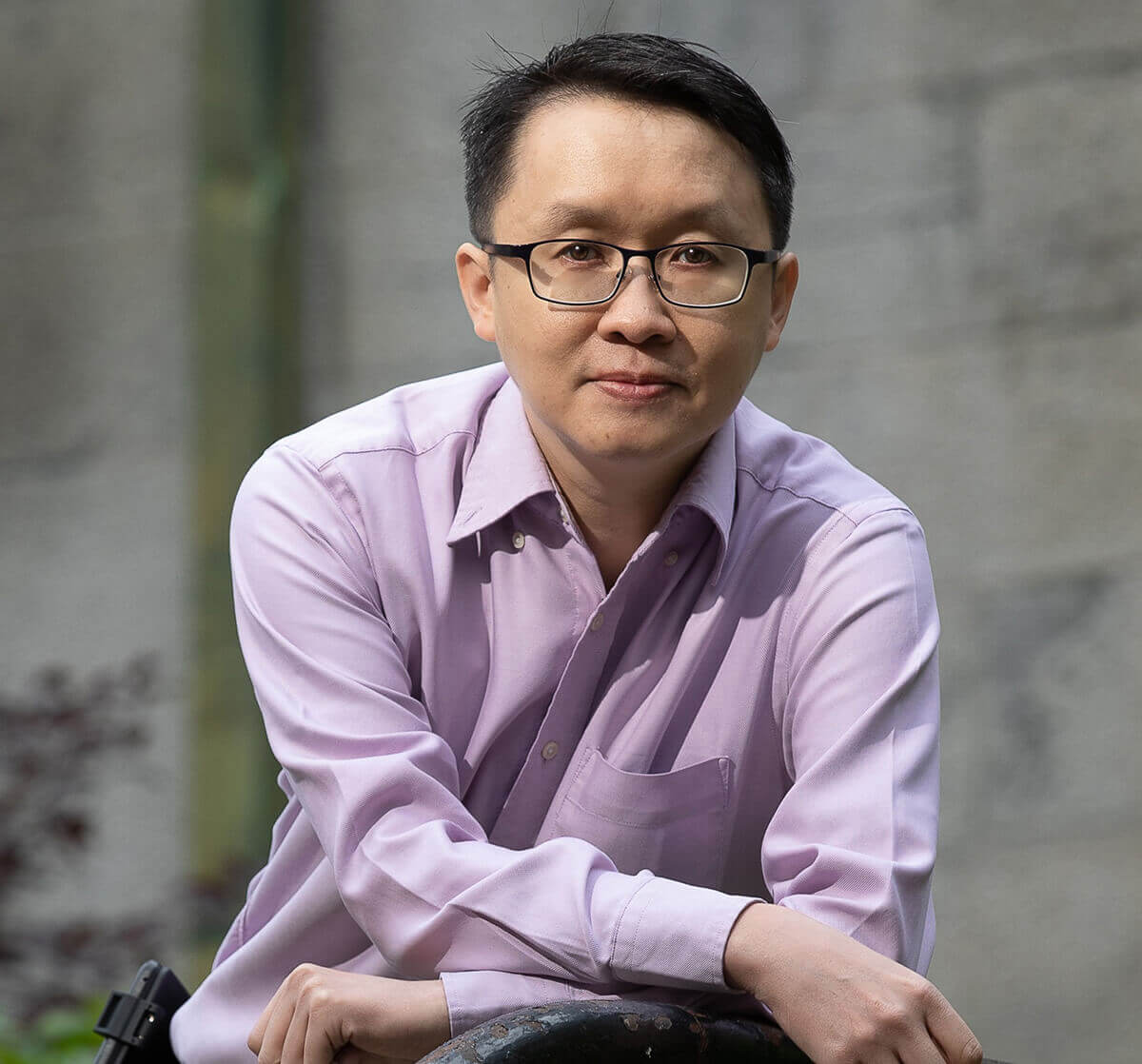 In this context, it seemed fundamental to us to bring the perspective of someone who is dedicated to this area of scientific research – we had the opportunity to speak to Dr. Benjamin Fung, professor in the School of Information Studies and a Canada Research Chair in Data Mining for Cybersecurity.
In this context, it seemed fundamental to us to bring the perspective of someone who is dedicated to this area of scientific research – we had the opportunity to speak to Dr. Benjamin Fung, professor in the School of Information Studies and a Canada Research Chair in Data Mining for Cybersecurity.
Milénio Stadium: Wars are no longer fought only with tanks, armies on the ground and missiles. They also take place in the “trenches” of the Internet. Are the cybersecurity systems of the fundamental structures of the various countries prepared for an effective defence against possible attacks?
Dr. Benjamin Fung: The attack on Ukraine shows a typical hybrid warfare with multi dimensions. Most of the attacks are in the category of distributed denial of services (DDoS), which the objectives to bring down the target systems. This wave of cyberattacks targets both military and non-military targets known Operational Technology (OT) systems, such as utilities, water systems. Since DDoS attacks are popular in recent years, many critical cyber infrastructures can sustain a certain level of attacks. Yet, many IT/OT systems are not well prepared to defend state-sponsored large-scale DDoS attacks. It is possible that the pro-Russian hacktivists may target EU in the next few weeks, but the targets will be carefully chosen, e.g., financial services, government agencies, etc.
MS: To the Russian attacks against several computer systems of several European countries and, mainly, Ukrainian ones, the hacker group “Anonymous” has responded with a declaration of cyberwar against Russia. Will this situation, with this group that has always been seen and treated as “criminal” become a kind of modern-day Robin Hood?
BF: The group “Anonymous” has claimed responsibility for 1500 cyberattacks on the Russian and Belarusian governments. The group has been the kind of modern-day Robin Hood in various democratic movements, e.g., the democratic movement in Hong Kong in 2014.
MS: Have recent events shined a spotlight on the need to have strong cybersecurity systems in place?
BF: Government agencies should carefully review and re-examine the critical cyber-physical infrastructures in their countries with the consideration of state-sponsored cyber warfare. It is difficult to require every IT/OT systems to reach the same level of robustness, but at least re-examine the critical ones.
MS: Besides cyberattacks on various entities considered key, there is another way of using the internet as a war stage. The so-called fake news can have a very strong effect, namely on social networks. What recommendations can you give to the common user of social media platforms, so that they are not “used” in this form of war?
BF: Disinformation plays an important role in this hybrid warfare. Common social media users are often being trapped in the vicious cycle of reinforced information consumption patterns. We always need to use critical thinking to analyze a piece of information, especially if it is coming from less trustworthy sources. In this attack, although most of us are not directly involved in the war, we are indeed part of the targets of disinformation attack. The Russian government tries to project an image that Ukraine is weak and their attack is very successful. Many Chinese social media in fact contributes to the spread of disinformation. I am sure you have watched a video that shows a Ukraine father sent his kid and wife to a bus while he stayed behind to fight against the Russians. In the Chinese social media, that video has been intentionally misinterpreted as a Russian father leaving his family to liberate Ukrainians.
MS: As an expert in the area of cybersecurity, what do you fear most in this war between Russia and Ukraine?
BF: If Ukraine falls and all other countries remain imposing financial sanctions only, this will set a very bad example in the international community. For example, another dictatorial regime, China, may consider invading Taiwan, which is the world factory of semiconductors. The negative impact will be much larger than the impact on Ukraine. Japan, Australia, and the US will have no choice but to defend Taiwan. The scale of conflict will be at another level.
Another concern is on the information warfare. Disinformation has become a channel of foreign interference. (See: https://policyoptions.irpp.org/magazines/january-2022/misinformation-and-chinese-interference-in-canadas-affairs/). The US government is in the process of creating a Global Engagement Center to fight against disinformation. Canada should follow the same path.
MS: Is Canada properly “equipped” to fight eventual attacks to its computer systems?
BF: As the number and scale of cyberattacks continue to grow, many agencies, organizations, and companies have significantly improved their cyber resilience via regular patching, training, testing, and continuous monitoring. Compared to 5 years ago, I would say the security of some of our critical systems has improved. Yet, it is difficult to completely prevent cyberattacks initiated by state-sponsored actors. We can improve the robustness of our systems so that in case there is an attack, we aim at fast system recovery.








Redes Sociais - Comentários